Overview
Firmware Over-The-Air (FOTA) updates are critical to modern IoT product lifecycles — enabling remote bug fixes, feature rollouts, and security patches without physical access to deployed devices. The following case studies demonstrate Z-Crossing Solutions’ expertise in designing robust, integrity-verified FOTA systems across multiple hardware platforms, protocols, and connectivity technologies.
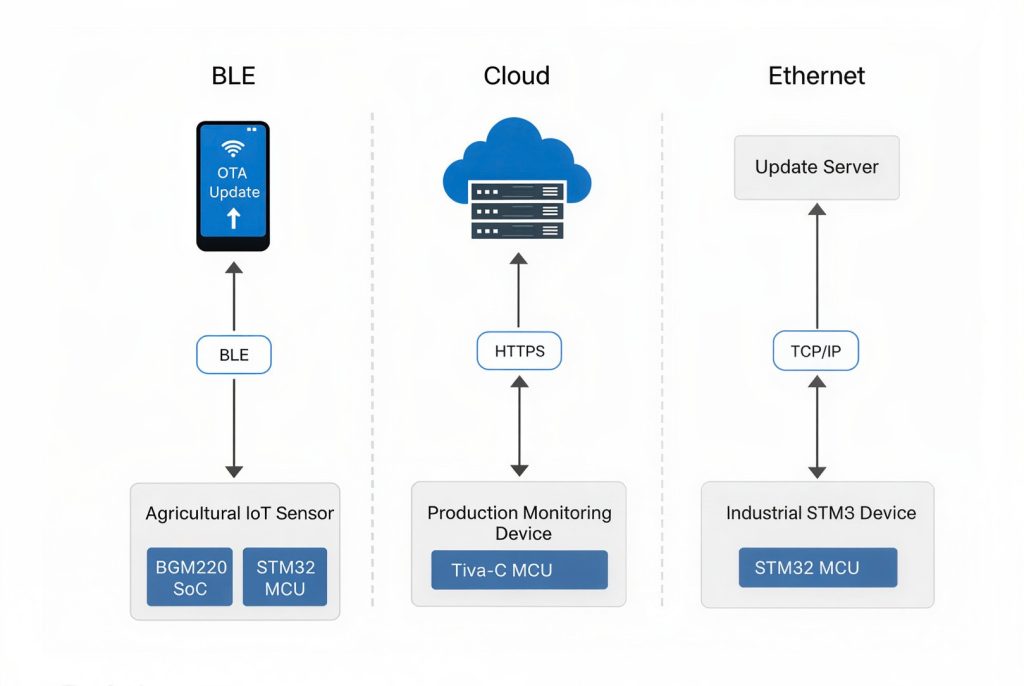
Case 01 Agricultural IoT Device
BLE-based wireless firmware update via mobile application
Hardware
- STM32F4xx MCU
- BGM220 SoC (Silicon Labs)
Stack & Protocols
- Embedded C
- BLE
- UART
- CRC Verification
- Custom Protocol
Update Flow
- Mobile application authenticates with the BGM220 BLE SoC before any firmware data is exchanged.
- Firmware binary is streamed to the BGM220 over BLE in chunks using a custom communication protocol.
- BGM220 forwards each firmware chunk to the STM32 master MCU via UART.
- STM32 computes a CRC checksum over all received firmware data and compares it against the CRC value sent by the mobile app.
- Firmware is written to internal flash only after CRC verification passes — ensuring complete integrity before installation.
Key Outcome: End-to-end authenticated and integrity-checked OTA for field-deployed agricultural sensors — no physical access required for firmware maintenance.
Case 02 Production Monitoring System
Secure HTTPS-based cloud FOTA with recovery firmware support
Hardware
- TM4C Tiva-C MCU
- External Flash Memory
Stack & Protocols
- Ti-RTOS
- NDK Stack
- HTTPS
- WolfSSL
- CRC Verification
Update Flow
- On boot or update check, the device sends its unique MAC ID to the server for device-specific firmware lookup.
- Server responds with firmware metadata: serial number, firmware size, filename, and a secure download link.
- Device downloads the firmware securely over HTTPS using WolfSSL, ensuring encrypted transmission.
- CRC checksum is computed locally and validated against the server-provided checksum before any flash write occurs.
- Flash is partitioned for Bootloader, Application, Update FW, and Recovery FW — ensuring safe rollback if an update fails.
- Update process safely resumes after connectivity interruptions, preventing bricked devices in the field.
Key Outcome: Production floor devices stay up-to-date via cloud with zero downtime risk — recovery firmware guarantees a safe fallback state.